Tor, Anonymity Online
Introduction
Tor with Gargoyle provides plug and play anonymous access to the internet. Routers running Gargoyle 1.5.1 and above with a USB port have support Tor. It can be run on a router with 32MB of memory only if SWAP is enabled, but 64MB is recommended.
Recommended routers include
- Ubiquiti Routerstation
- Ubiquiti Routerstation Pro
- Buffalo WZR-HP-G300NH
- Netgear WNDR3700v1-2
About
Tor prevents anyone from learning your location or browsing habits. Tor is for web browsers, instant messaging clients, remote logins, and more. Tor Protects your privacy. Defend yourself against network surveillance and traffic analysis.
Tor Security
NOTE: Tor can't solve all anonymity problems.
It should be noted that you should NOT run bittorrent through Tor – not only does anonymization not work for bittorrent, it can expose your identity in any other traffic you run through Tor.
Tor Speed
You need to realise that Tor is never going to be blazing fast. Your traffic is bouncing through volunteers' computers in various parts of the world, and some bottlenecks and network latency will always be present. You shouldn't expect to see university-style bandwidth through Tor.
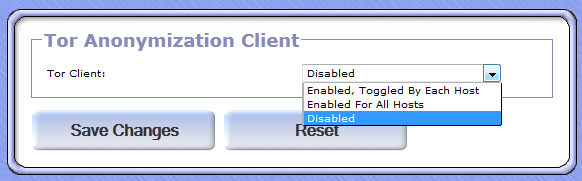
Set-up
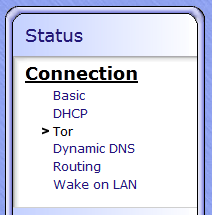
Tor Client:
Enabled, Toggled By Each Host
Every client that wants to be protected must select enable at the Gargoyle router login screen.
Enable For All Hosts
All clients are protected by Tor
Protocols Not Handled By Tor:
Some Protocols may bypass Tor therefore compromise your Anonymity.
Select either
Ignore
All services will work but your Anonymity may be less
Block
Anonymity will be improved but some services may no longer work.
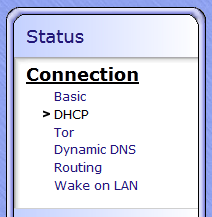
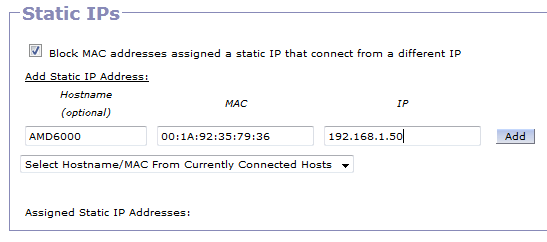
Enabled, Toggled By Each Host (Per IP address)
To enable by each host (Per IP address) you must set a static IP address per host.
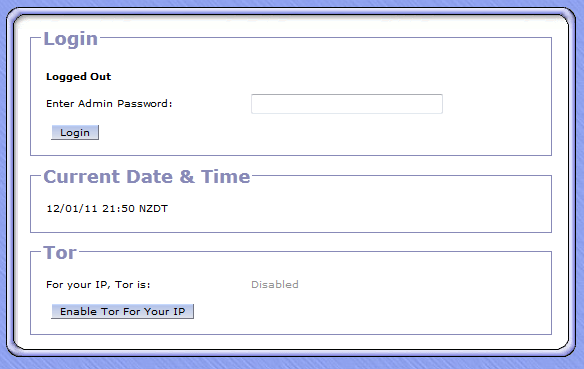
Once the host (Client PC) has a fixed IP address log out and reconnect to Gargoyle and you should get this screen
Click “Enable Tor for Your IP” and you should be protected.
Check Tor
I would suggest you test that your router is working properly by visiting “Check”
Check determines if you are successfully browsing with Tor.
Tor Hidden Services
Tor Hidden Services are one of the best features of Tor, and one that most people aren't aware of. Basically, a Tor hidden service is one provided by a server located/hosted inside, the Tor network. This ensures anonymity for both the connecting client and the server.
In general, Tor takes your connection, bounces it around inside the Tor network, and then forwards it to its ultimate destination so that whatever host you're connecting to only sees your address as the the last Tor node visited (the exit node). The address you're connecting to, though, is publicly known – it's on an IP address that everyone can get to. If someone wants to know where the server is located, that's easy to do.
When connecting to a tor hidden node, the connection never leaves the Tor network. There are addresses that look like fairly random strings of alphanumeric characters and that end in “.onion” that are only accessible if you're connected through Tor. Since the server is accessible only through Tor, the location of the server can not be tracked down, allowing for communication to take place between two parties, both of whom are effectively anonymized.
For example, Tor Mail: http://jhiwjjlqpyawmpjx.onion Truly anonymous email – accessible anonymously, and no way to know where the server is, so it would be hard to take down.
Here's another forum service called “TorSquare”, that's basically an anonymous forum: http://ajqaivfxtqy3fdlr.onion/torsquare/
Google for more “.onion” addresses and you'll find a bunch posted around the web.
The new “Hidden Service Only” mode does exactly what it says – it allows (anonymous) access to these Tor hiddens services, while all other traffic bypasses Tor. This means that if you're connecting to a rather mundane website like gargoyle-router.com, you'll get a nice, fast connection (Tor tends to crawl), without anonymity protection. But, if you want to access one of these hidden service addresses, you will be able to, and you will be anonymous while doing so.
In addition to the “Hidden Service Only Mode”, Tor hidden services will also work in “Tor Enabled for All” mode and when Tor is active for individual hosts. In the latest version, hidden services will not be available in the case where tor is active for individual hosts, but currently turned off for a given host (Tor will have to be set active first). Note that Tor hidden services do not work in 1.5.2, this feature has only been introduced in the latest commits to the master branch of the repository.
Most people probably shouldn't need to touch the “Tor hidden subnet” and “Tor hidden subnet mask” parameters. They're only there because if the LAN or WAN uses the same (reserved) subnet as what is specified here, you'll have problems/conflicts with Tor hidden services. Just make sure this subnet is outside whatever you're using for your main connection and it will work.